Pro-Russian Hackers KillNet Try to Access FMCSA Portal
FMCSA said none of its internal systems were compromised but advises that everyone who uses its portal to change their passwords immediately.
The Federal Motor Carrier Safety Administration has confirmed that an outside group known as KillNet has been trying to access its public portal using stolen user passwords.
The agency uses 13 web-based applications, to aid vehicle registration, inspections, compliance monitoring and enforcement. Many of FMCSA’s information systems contain sensitive data, including personally identifiable information.
As seen by Hackread.com, the hacker group claimed to have broken into the FMCSA’s public portal.
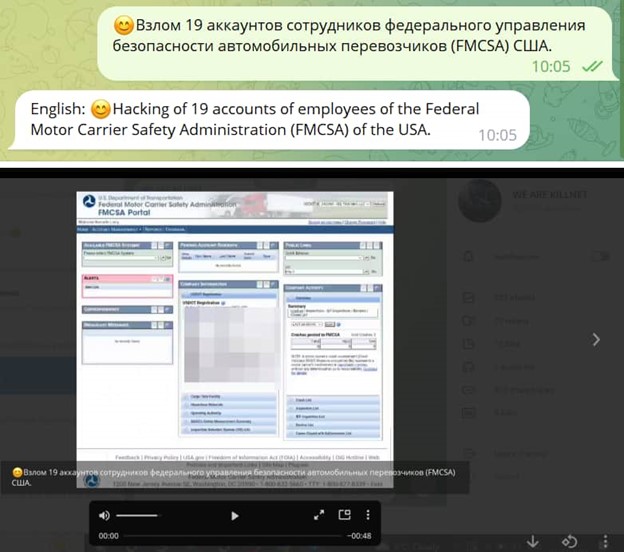
“While KillNet’s attacks usually do not cause major damage, they can cause service outages lasting several hours or even days,” according to an alert. “The group should be considered a threat to government and critical infrastructure organizations, including healthcare.”
In addition, Killnet said it had infiltrated the FBI’s database, allegedly stealing the personal information of more than 10,000 U.S. federal agents, the White House websites, and temporarily took down SpaceX’s Starlink satellite service used in Ukraine to help defend the country and maintain stable communications.
FMCSA is advising everyone who uses its portal to change their passwords immediately.
FMCSA prepared at-risk IT infrastructure for hacking risk
Back in October 2021, an audit concluded that FMCSA’s IT infrastructure was fraught with security weaknesses and was at risk by hackers and malware.
“We found several agency web servers which allowed us to gain unauthorized access to FMCSA’s network,” the audit said. “FMCSA did not detect our access or placement of malware on the network in part because it did not use required automated detection tools and malicious code protections.”
“We also gained access to 13.6 million unencrypted personally identifiable information records,” auditors said. “Had malicious hackers obtained this PII, it could have cost FMCSA up to $570 million in credit monitoring fees.”
FMCSA agreed with the audit’s 13 recommendations and planned to fix them by November 2022. According to the report, all 13 recommendations had been completed.
This may have helped prevent further damage by Killnet’s attempt to access the FMCSA portal.
What Should Carriers Do?
FMCSA is advising everyone who uses the FMCSA portal to change their passwords immediately.
FMCSA’s security policies and processes must adhere to departmental policies and National Institute on Standards and Technology guidelines. This requires users to:
- Choose strong passwords that are at least 12 characters long and have a combination of letters (upper and lower case), numbers, and special characters
- Protect passwords and personal identification numbers for log-ons from disclosure, not record passwords or access control numbers on paper or in electronic form, or store them on or with DOT workstations, laptop computers or portable electronic devices
- Protect from spam emails by not providing any personal or departmental information solicited by email, forward to the appropriate DOT security help desk any email requesting such information or account or security settings verifications, and then delete the email.
Questions about DOT Compliance, Licensing, Audits, Programs, etc.?
Our DOT Specialists are here to help!
What are you searching for?
Is DOT Compliance your Top Priority?
Our DOT Compliance Programs ensure it is your top priority and keeps your business running.
Related Services
Subscribe to our Monthly Newsletter
Receive the latest transportation and trucking industry information about FMCSA and DOT Audits, Regulations, etc.
Related news
Trucking News
Get the latest trucking news on DOT Compliance, Licensing, Audits, and more!

How to Build a Digital DQF System for FMCSA Audits
Creating a digital DQF system is more than a technology upgrade—it’s a proactive strategy for reducing compliance risk, improving operational efficiency, and maintaining audit readiness.

FMCSA’s New Motus Registration System Is Live: What Motor Carriers Need to Do Now
The FMCSA has officially launched its long-awaited registration modernization platform: Motus: USDOT Registration System. For trucking companies, brokers, freight forwarders, and supporting service providers, this

Fuel Tax Trends in 2026: What Trucking Companies Need to Know About IFTA, Diesel Taxes, and Compliance
As diesel prices continue to fluctuate and lawmakers debate fuel tax relief measures, trucking companies across the country are paying closer attention to fuel tax
